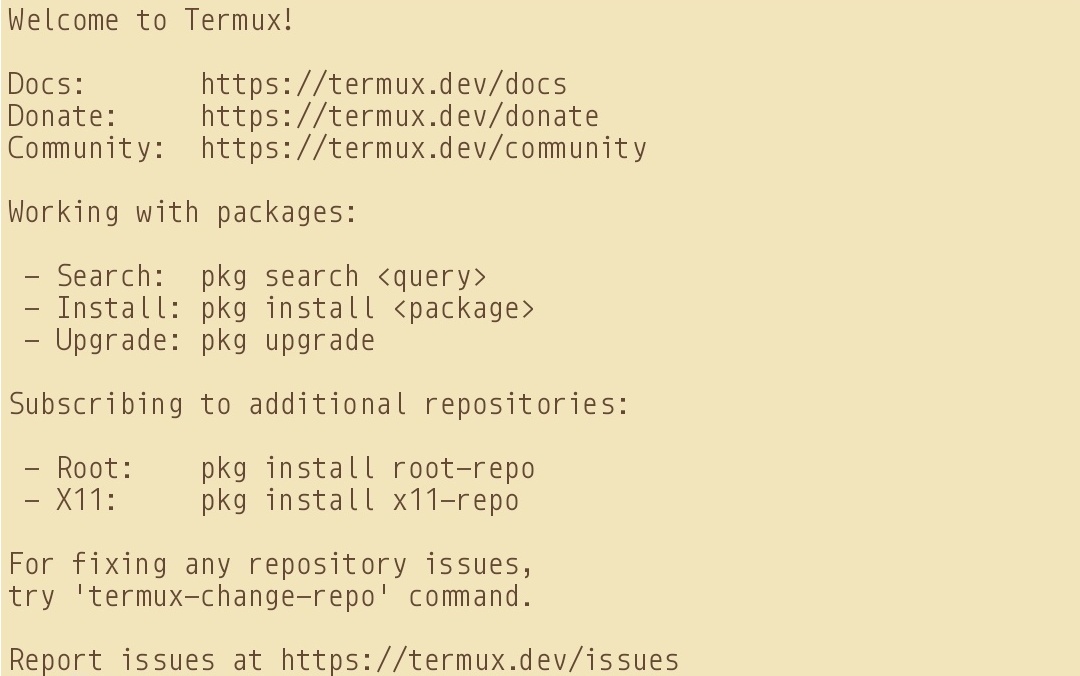
Install Termux & Termux Styling
Upgrade packages & install openssh and iproute2 on termux.Also, install root packages & busybox package if you need them.
pkg update -y && pkg upgrade -y
pkg install openssh -y
pkg install iproute2 -y
pkg install root-repo -y
pkg install busybox termux-services -y
If you like, you can also add the following termux repositories:
echo "deb https://grimler.se/termux-packages-24 stable main" > $PREFIX/etc/apt/sources.list
echo "deb https://grimler.se/termux-packages-24 stable main" > $PREFIX/etc/apt/sources.list.d/game.list
echo "deb https://grimler.se/termux-packages-24 stable main" > $PREFIX/etc/apt/sources.list.d/science.list
Ensure to setup the storage and stuff beforehand. See here: Setup Storage
Create SSH Private/Public Key Pair on Android - Termux
In our android device, we need to generate SSH key pair for connecting to SSH server the remote machine (example debian).
So, run the following command (this will also name the file as android for easy referencing):
ssh-keygen -t ed25519 -f id_ed25519_android
This will create the public & private key files in the ~/.ssh folder (/data/data/com.termux/files/homes/.ssh)
Send SSH Public Key to Remote Machine
Run cat ~/.ssh/id_ed25519_android.pub from termux which will return the public key for your android device.
It will be something like this:
ssh-ed25519 ABCDE1AaaA1aAAA1AAA1AAAAAAAAAaaaA1AaaAaaaAaaa1aAAAAaaAAAAaAaaaAAaaAA user@host
Now copy and paste this key to your remote machine either via the chat box option in the file transfer assistant app PlainApp or copying the id_ed25519_android.pub file across to your remote machine and then copy the content to ~/.ssh/authorized_keys file ($HOME/.ssh/authorized_keys).
Now kill any running sshd service by typing in termux: pkill -9 sshd. This is to let go of any cache or broken service pipes.
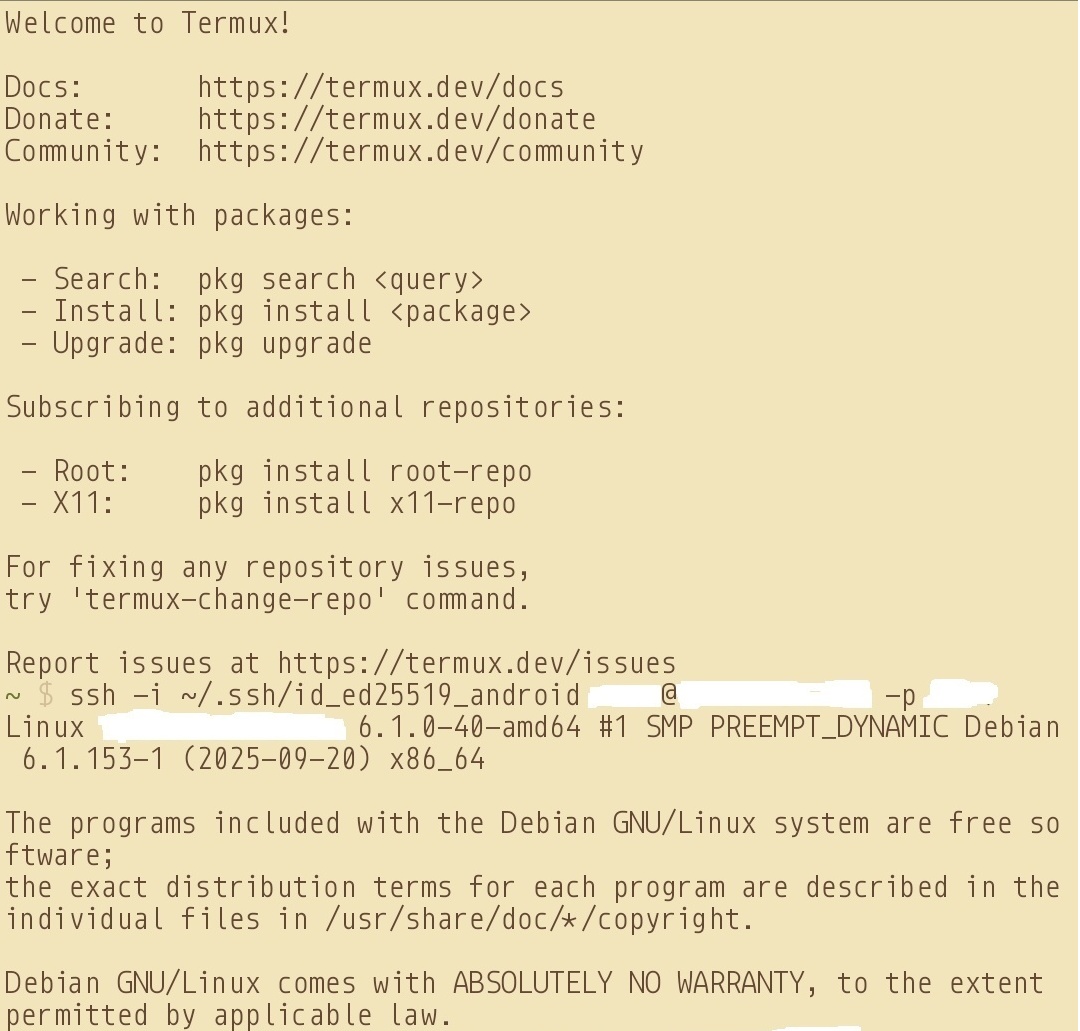
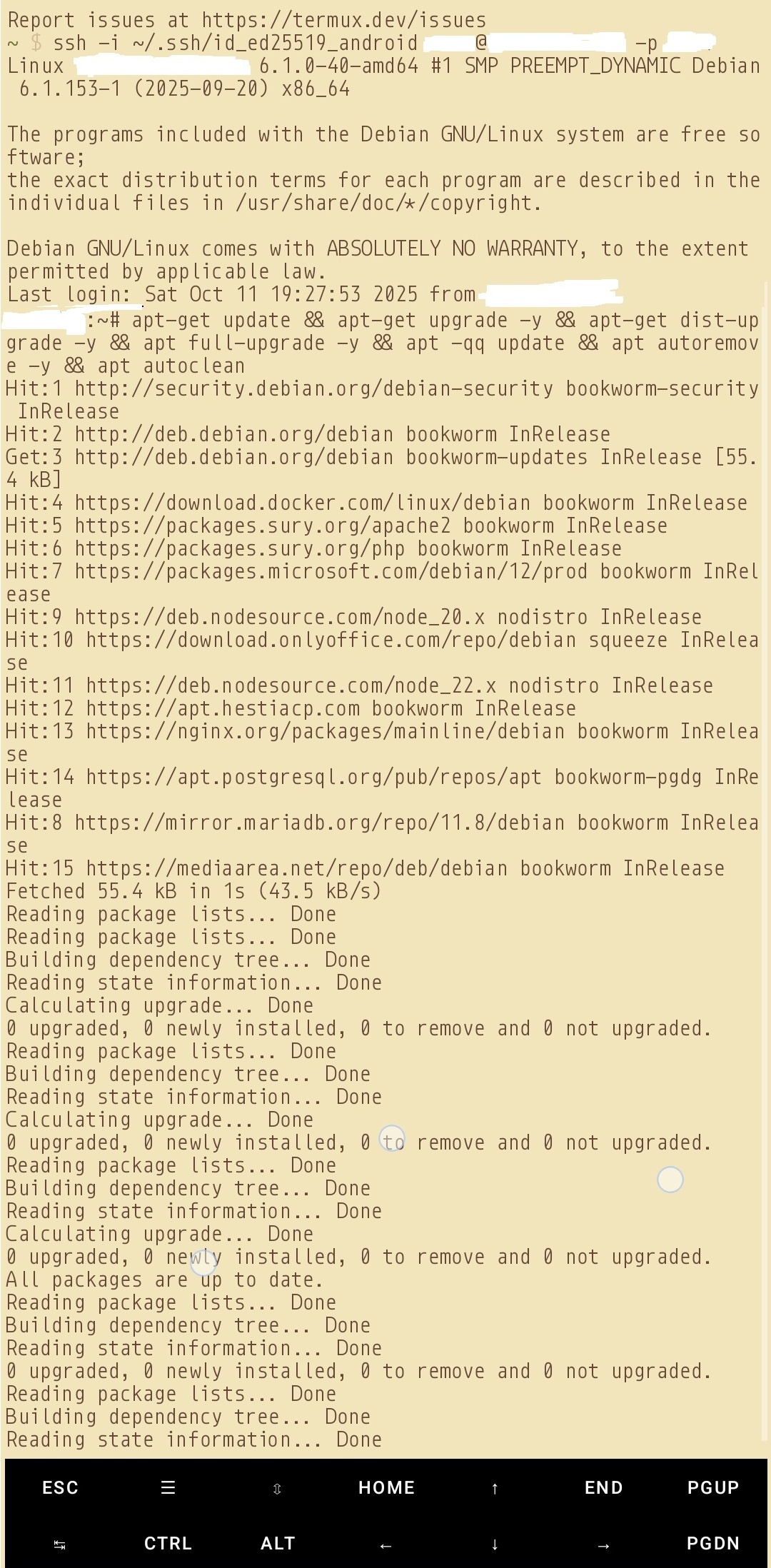
Now rerun sshd and connect to your remote server using the private key as pairing for the public key, via:
ssh -i ~/.ssh/id_ed25519_android user@host -p 1234
Sources & my own racking of 5 days:
Termux Wiki | Termux Repos | Some Logic
Sample images: